feat:🚩 Pico CTF 2025 Medium
feat:🚩 Pico CTF 2025 Medium
picoCTF 2025 Level: Medium
「Binary Instrumentation 1 : Reverse Engeneering」
- Description: I have been learning to use the Windows API to do cool stuff! Can you wake up my program to get the flag?
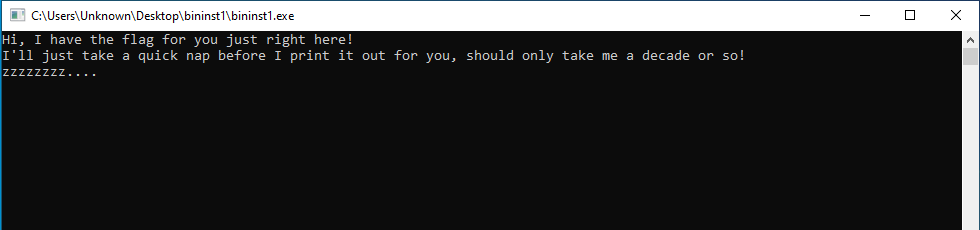
exeファイルをダウンロードし,実行すると下記の文言が表示されそれ以外の処理はなされません.
ヒント通りに,Frida を使用して Sleep 関数のハンドラーを自動生成し,Sleep を解除するように改竄します.
__handlers__\KERNELBASE.dll\Sleep.js
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
/*
* Auto-generated by Frida. Please modify to match the signature of Sleep.
* This stub is currently auto-generated from manpages when available.
*
* For full API reference, see: https://frida.re/docs/javascript-api/
*/
defineHandler({
onEnter(log, args, state) {
// args[0] はミリ秒(DWORD)
const orig = args[0].toInt32();
log("[*] Sleep called, original ms = " + orig);
// スリープ時間を 0 に書き換える(即時復帰)
args[0] = ptr("0");
log("[*] Sleep bypassed -> set ms = 0");
},
onLeave(log, retval, state) {
// 何もしない
},
});
Windows10 VM に Python の venv を導入して,Frida を導入しています.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
(venv) C:\Users\Unknown\Desktop\venv> frida-trace -f "C:\Users\Unknown\Desktop\scan_exclusion_folder\bininst1.exe" -i "Sleep"
Instrumenting... e`...
Sleep: Loaded handler at "C:\Users\Unknown\Desktop\venv\__handlers__\KERNELBASE.
dll\Sleep.js"
Sleep: Loaded handler at "C:\Users\Unknown\Desktop\venv\__handlers__\KERNEL32.DL
L\Sleep.js"
Started tracing 2 functions. Web UI available at http://localhost:50083/
Hi, I have the flag for you just right here!
I'll just take a quick nap before I print it out for you, should only take me a
decade or so!
zzzzzzzz....
Ok, I'm Up! The flag is: cGljb0NURnt3NGtlX20zX3VwX3cxdGhfZnIxZGFfZjI3YWNjMzh9
/* TID 0x188c */
31 ms Sleep()
31 ms | [*] Sleep called, original ms = -2
31 ms | [*] Sleep bypassed -> set ms = 0
:
:
:
31 ms Sleep()
31 ms | [*] Sleep called, original ms = -2
31 ms | [*] Sleep bypassed -> set ms = 0
Process terminated
表示された base64 エンコード文字列を base64 デコードすると,Flag を入手できました.
- Parrot terminal
1
2
$ echo "cGljb0NURnt3NGtlX20zX3VwX3cxdGhfZnIxZGFfZjI3YWNjMzh9" | base64 -d
picoCTF{w4ke_m3_up_w1th_fr1da_f27acc38}
「Binary Instrumentation 2 : Reverse Engeneering」
- Description: I’ve been learning more Windows API functions to do my bidding. Hmm… I swear this program was supposed to create a file and write the flag directly to the file. Can you try and intercept the file writing function to see what went wrong?
Easy だと分かりやすい問題が多かったですが,この問題には苦戦しました…
File が含まれる関数(KERNEL32 のみ)を抽出します.
CreateFileA が使用されていることが分かりました.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
(venv) C:\Users\Unknown\Desktop\venv> frida-trace -f "C:\Users\Unknown\Desktop\scan_exclusion_folder\bininst2.exe" -i *File* -X "KERNEL32"
Warning: Skipping "FreeEncryptedFileMetadata": unable to intercept function at 00007FFFCEB29580; please file a bug
Warning: Skipping "_CrtSetReportFile": unable to intercept function at 00007FFFCF5A7BF0; please file a bug
Started tracing 546 functions. Web UI available at http://localhost:60691/
/* TID 0x1bec */
3528 ms NtDeviceIoControlFile()
3528 ms RtlDosApplyFileIsolationRedirection_Ustr()
3528 ms RtlDosApplyFileIsolationRedirection_Ustr()
3528 ms RtlDosApplyFileIsolationRedirection_Ustr()
3528 ms NtQueryAttributesFile()
3528 ms NtQueryAttributesFile()
3528 ms NtOpenFile()
3528 ms RtlDosApplyFileIsolationRedirection_Ustr()
3544 ms GetSystemTimeAsFileTime()
3544 ms | GetSystemTimeAsFileTime()
3544 ms GetModuleFileNameW()
3544 ms | GetModuleFileNameW()
3544 ms AreFileApisANSI()
3544 ms | AreFileApisANSI()
3544 ms CreateFileA()
3544 ms | CreateFileA()
Process terminated
このインスタンスは未攻略です.
This post is licensed under CC BY 4.0 by the author.